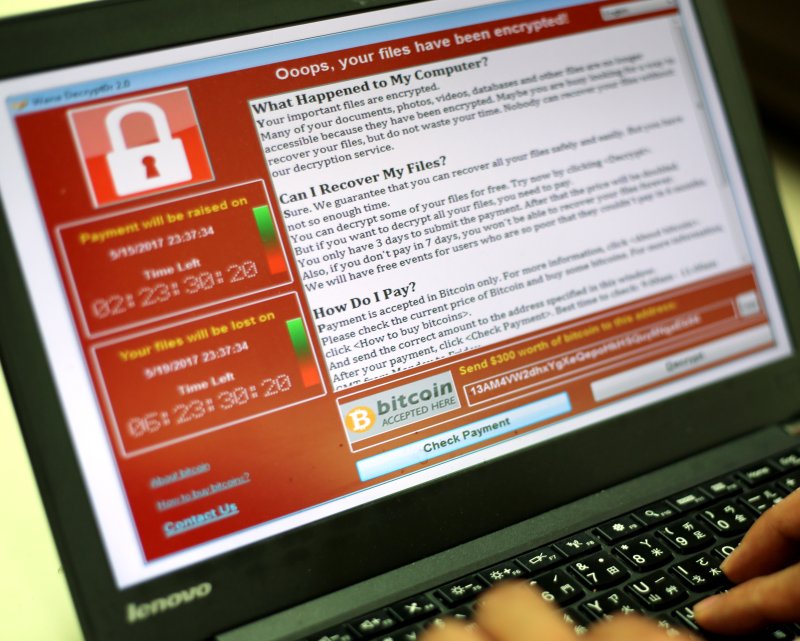
A programer shows a sample of a ransomware cyberattack on a laptop in May. The hackers behind the WannaCry cyberattack have moved the ransom money from three bitcoin accounts to larger accounts. File Photo by Ritchie B. Tongo/EPA
Aug. 3 (UPI) -- The hackers behind May's WannaCry cyberattack have moved the ransom money they accumulated from three bitcoin accounts to other, larger accounts, online tracking records show.
The WannaCry attack paralyzed business and government computer systems across the world by exploiting security flaws first unearthed by the National Security Agency. Among the groups hardest hit were the Spanish telecom giant Telefonica and Britain's health ministry. Hospitals in Britain were forced to turn away patients for multiple days while officials scrambled to regain control of their computer systems.
Though the hackers, who are believed to have ties to North Korea, succeeded in upending cybersecurity systems across the world, their efforts to turn it into a money-making scheme largely failed due to their own ineptitude.
For starters, though bitcoin transactions are public, they are also anonymous. The three accounts the hackers set up to receive ransom payments from victims were unable to track who had made the payments, meaning the decryption codes the hackers promised were unreliable, making it less likely victims would be willing to pay the ransom in the first place. Other basic coding errors made some of the system take-overs easily remedied.
In another twist, the hackers set up a free email account to communicate with victims that was almost immediately identified by the service provider and shut down.
In all, the hackers received about $140,000 in ransom money in the form of bitcoin payments. Even that payment was inflated due to the rising value of bitcoin in the months since the WannaCry attack. At the time, they received less than $100,000 in ransom payments.
International trackers set up a Twitter account to monitor and report any movement in the three accounts the hackers used. On Thursday, that account noted the accounts were drained and the bitcoins were transferred into larger joint accounts known as mixers. Though the bitcoin can still be tracked, mixers allow users to break up bitcoin transactions into smaller ones that are more difficult to trace.
Europol, the European investigative agency, declined to comment on the status of the WannaCry investigation. The U.S. Justice Department did not immediately respond to comment.
On Thursday, authorities in Las Vegas arrested Marcus Hutchins, a British computer security researcher responsible for stopping May's WannaCry attack. An indictment filed in the U.S. District Court in Wisconsin accused him of distributing the banking malware known as Kronos between July 2014 and July 2015, USA Today reported.
Hutchins was in Las Vegas for two computer security conferences -- Black Hat and Defcon.