The hackers were participating in the Pentagon's first "bug bounty," where it asked those with computer hacking capabilities to investigate five public websites and identify potential lapses in security where a nefarious hacker could do damage. If those participating identify a legitimate security breach, they earn a bounty.
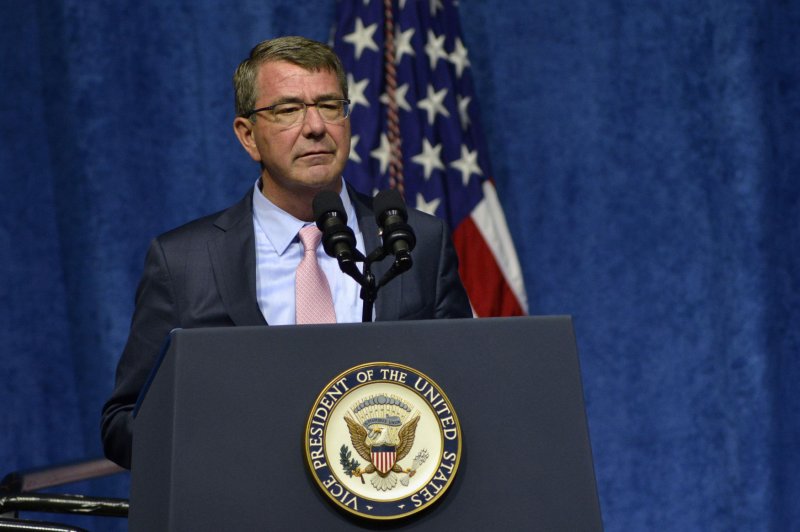
"We know that state-sponsored actors and black-hat hackers want to challenge and exploit our networks," Carter said. "What we didn't fully appreciate before this pilot was how many white-hat hackers there are who want to make a difference -- hackers who want to help keep our people and nation safer."
More than 1,400 eligible hackers registered for the federal government's first "bug bounty" and identified 138 different potential security lapses.
The Pentagon said hiring a private firm to evaluate and fix potential security risks could have cost taxpayers more than $1 million, but by crowd-sourcing the work, it spent only $150,000 in bounty money, and to fix the security lapses combined.
None of the Pentagon websites included in the bounty were related to the department's classified or critical operations, officials said.